Cyber Insurance for Small Businesses: Coverage, Costs, and How to Choose
Outline
– Coverage essentials and why it matters
– Costs, pricing drivers, and realistic budgets
– Policy terms to compare and common pitfalls
– Risk controls insurers reward and how they reduce loss
– How to select limits, buy coverage, and handle a claim
What Cyber Insurance Covers and Why Small Businesses Need It
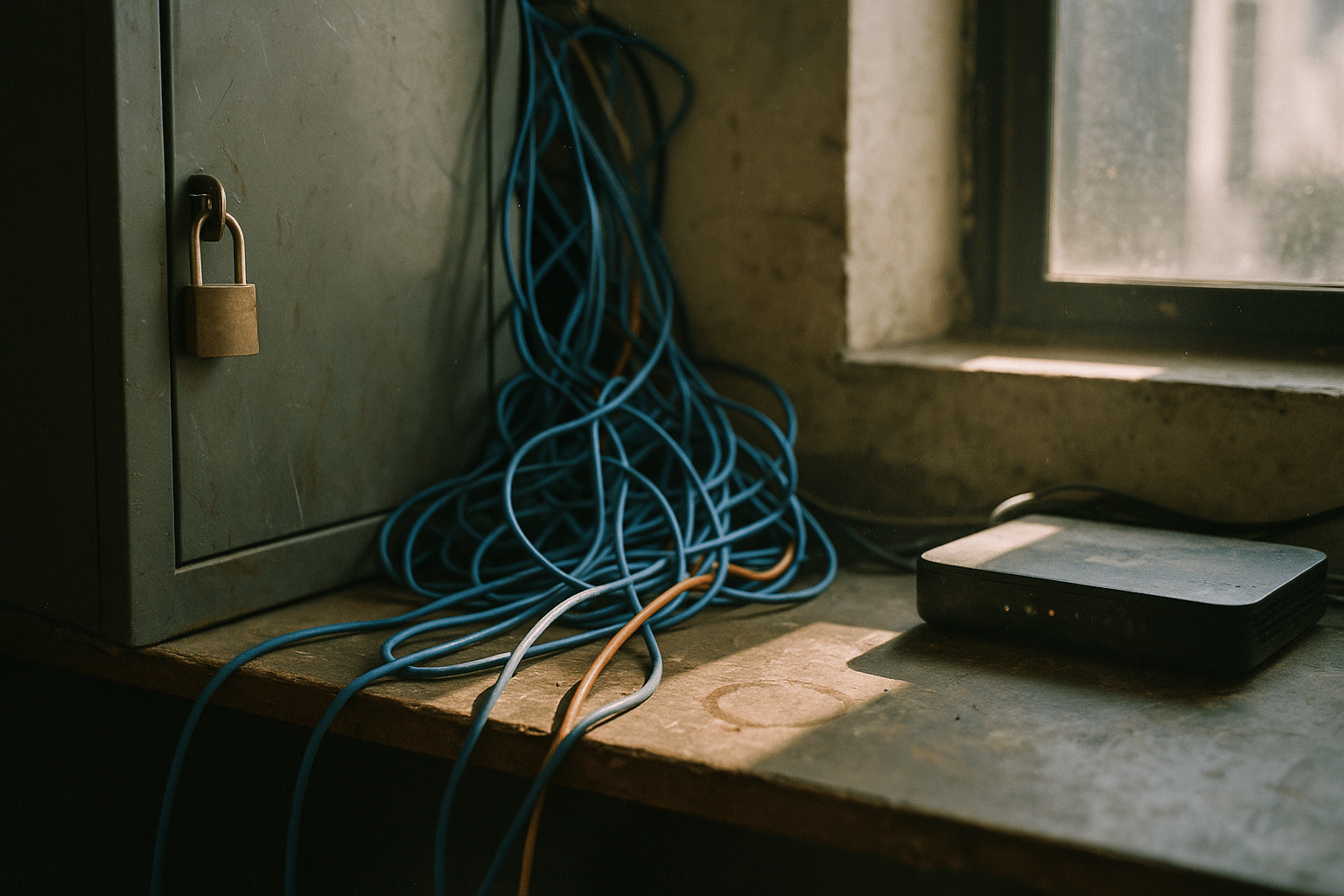
Cyber insurance exists to keep an incident from turning into a company‑ending event. For small businesses, the stakes are high: a single ransomware lockout can halt orders, payroll, and customer service in the same hour. While no policy replaces strong security, it can fund the experts and time you need to recover. Think of it as a seatbelt for your balance sheet—quiet in the good times, stabilizing when everything lurches forward.
Most policies split into two broad buckets. First‑party coverages handle direct costs your organization incurs during and after an incident. Typical components include:
– Incident response coordination and legal counsel to guide decisions and preserve privilege
– Digital forensics to identify entry points, affected systems, and scope
– Data restoration and system recovery to rebuild servers, endpoints, and applications
– Business interruption to replace lost net income during downtime, plus extra expense to speed recovery
– Cyber extortion support and negotiated payments where lawful, including assistance to verify credibility and avoid double extortion
– Notification, call center, and identity monitoring for affected individuals when personal data is exposed
Third‑party coverages address liabilities to others. These may include:
– Network security and privacy liability for claims that your systems enabled a breach or outage affecting customers or partners
– Media liability for unintentional IP or content issues online
– Regulatory defense and certain fines or penalties where permitted by law, triggered by privacy rules and breach reporting duties
Why it matters for small enterprises: threat actors target convenience, not just size. Many attacks begin with a single phish, unpatched software, or a reused password. Industry studies frequently note that the human element features in a majority of incidents, and downtime costs accumulate quickly—lost sales, overtime for remediation, and strained customer relationships. Cyber insurance can also unlock vetted vendors at negotiated rates, accelerating triage when minutes count.
Consider a straightforward scenario. An accounting firm’s file server is encrypted overnight, and the attacker threatens to leak client records. The firm engages breach counsel via the policy, kicks off forensics, restores from backups, and coordinates required notifications. Business interruption coverage cushions two weeks of reduced operations while systems are rebuilt. Without a policy, each of those steps still needs doing—only now they land entirely on your cash flow and calendar.
What It Costs: Pricing Drivers, Examples, and Budgeting
Premiums for small businesses vary widely, but a practical way to think about cost is to start with exposure rather than headlines. Underwriters look at what could be monetized or disrupted: revenue, the volume and sensitivity of data, reliance on third‑party platforms, and the maturity of your controls. In recent years, many small firms with solid hygiene have seen annual premiums range from the low hundreds to a few thousand dollars for entry‑level limits, while larger limits, higher‑risk sectors, and prior losses push premiums higher.
Key drivers you can influence include:
– Multi‑factor authentication coverage: presence across email, remote access, admin access, and backups
– Backup posture: immutable, offline copies with regular testing versus single‑copy or cloud‑only
– Patch cadence and end‑of‑life systems: how quickly critical vulnerabilities are remediated
– Endpoint protection and monitoring: ability to detect lateral movement and privilege escalation
– Email security and training: filtering, impersonation controls, and practical simulations
Other pricing components you will encounter:
– Limits and sublimits: overall aggregate (for example, 1M) and smaller caps for ransomware, social engineering, or dependent business interruption
– Retentions (deductibles): higher retentions usually reduce premium; align with your tolerance to self‑fund smaller events
– Industry and revenue: payment processors, healthcare, and professional services often carry distinct risk profiles due to data sensitivity and contractual obligations
– Claim history: a clean record helps; a recent loss can prompt higher rates and conditions until controls improve
To budget, map cost against plausible incident scenarios. For many small firms, direct incident response can reach tens or even hundreds of thousands of dollars once forensics, restoration, legal guidance, and notification are tallied. Add downtime, overtime, and vendor rush fees, and the bill can grow quickly. Insurance aims to steady these spikes. A practical approach is to estimate one to two weeks of disrupted operations and ask: if that happened tomorrow, what would keeping the lights on cost? Use that figure to evaluate whether a 500k, 1M, or higher limit fits your needs and cash reserves.
Example: A retail operation with 3M annual revenue, cardholder and loyalty data, and lean IT adopts strong controls. It might see quotes in the four‑figure range for a 1M limit with a moderate retention. The same business without MFA, with unsupported systems, and recent phishing losses could face materially higher pricing, narrower terms, or even a declination. Price is not the only lens; how coverage responds under stress will matter more than the last dollar saved on premium.
Reading the Fine Print: Clauses, Exclusions, and Negotiation Tips
The difference between a claim paid smoothly and a frustrating surprise often hides in definitions and sublimits. Start with coverage triggers. Some policies require a “network security failure,” while others respond to a “privacy event” or “system failure.” Broader formulations can capture more scenarios, such as outages caused by human error or a failed update, not just malicious acts. Similarly, check whether “computer system” includes cloud services and managed providers; many small businesses live in the cloud and need those dependencies clearly in scope.
Important clauses and features to compare:
– Retroactive date: ideally, coverage looks back to unknown events that may have begun before policy inception; a retro date too recent narrows protection
– Business interruption waiting period: common ranges are 8–24 hours; shorter waits mean earlier coverage for lost income
– Dependent business interruption: extends BI to outages at critical vendors; confirm named or unnamed dependencies and sublimits
– Ransomware terms: coinsurance or sublimits may apply; look for coverage of data restoration, negotiation services, and hardware “bricking” where offered
– Social engineering and funds transfer fraud: distinct insuring agreements with their own triggers; verify bank verification conditions and call‑back controls
Typical exclusions deserve a careful read:
– Prior known incidents and deliberate acts by senior leadership
– Bodily injury and property damage not tied to a covered cyber peril
– Contractual liability assumed beyond your negligence
– Infrastructure or utility failures not caused by you or a covered cyber event
– Broad “war” or “hostile acts” language; seek wording that focuses on major nation‑state conflicts rather than everyday criminal activity
Negotiation is possible, especially when you demonstrate control maturity. You can request higher sublimits for areas that match your risk, add clarity around cloud providers, or tighten definitions that could block a claim. Ask how panel vendors are selected, whether you may use pre‑approved local partners, and how consent‑to‑settle works. A cooperative framework speeds response when the phone rings at 2 a.m. Finally, align retentions with your rainy‑day fund: retain what you can comfortably self‑fund, and insure the rest. The goal is resilience, not perfection.
Security Wins That Lower Risk and Strengthen Your Application
Insurers increasingly evaluate controls with the same seriousness that lenders apply to credit history. That shift is good news for disciplined small businesses, because straightforward improvements can meaningfully reduce both incident likelihood and claim severity. The core theme: reduce the blast radius. If a single click or compromised password can’t roam freely, an attacker’s day gets longer and your recovery window gets shorter.
Prioritized controls that punch above their weight:
– Multi‑factor authentication on email, remote access, administrator accounts, and backup consoles to blunt credential theft
– Endpoint protection with behavioral detection, isolation, and remote response to contain spread
– Patch management that fast‑tracks critical fixes and retires unsupported systems
– Backups using a 3‑2‑1 approach with at least one offline or immutable copy, tested restores, and documented recovery time objectives
– Privileged access management and least privilege, restricting admin rights and recycling credentials regularly
– Email security that filters malicious attachments and flags impersonation, plus targeted staff training tied to real scenarios
– Logging and monitoring that centralize alerts so a single odd event does not hide in the noise
Beyond the tech, process matters. Maintain an incident response runbook: who calls whom, what to preserve, which systems to isolate, and how to communicate without tipping off an attacker. Tabletop exercises—short, focused drills—help reveal bottlenecks long before an alert fires. Vendor dependency mapping is critical: list your payment gateways, hosting providers, and line‑of‑business apps with emergency contacts and continuity plans. These steps not only harden your defenses but also speed up underwriting, as many applications now ask detailed control questions and may include automated external scanning.
Documentation is the quiet hero. Screenshots of MFA settings, backup reports, and patch dashboards show your posture rather than promise it. If you are early on this journey, start with one improvement each quarter and measure dwell time, phishing‑report rates, or patch cycles. Progress is persuasive. Insurers tend to reward it with broader terms and more favorable pricing. For your business, these same investments pay dividends whether or not you ever file a claim.
From Quote to Claim: Step‑By‑Step Buying Guide and Final Takeaways
Buying cyber insurance is less about chasing buzzwords and more about matching coverage to your actual operations. Begin with an inventory of data and systems. What customer or patient information do you hold, and where? Which applications generate revenue or fulfill orders? Estimate the financial impact of one day, one week, and two weeks of disruption. This anchors your limit and retention choices in your own numbers rather than generic averages.
A practical procurement sequence:
– Gather control evidence: MFA coverage, backup tests, patch policy, and staff training cadence
– Map critical vendors and integrations: identify “if this fails, we stop” dependencies
– Decide on a target limit and retention based on downtime scenarios and cash reserves
– Request quotes that specify triggers, definitions, sublimits, and waiting periods in plain terms
– Compare not only premium but vendor panels, claims support, and breadth of dependent business interruption
When quotes arrive, read using a “how would this pay?” mindset. Walk through a ransomware scenario and a vendor outage scenario line by line: which insuring agreements respond, when does business interruption start, and what sublimits might cap recovery? If an item is unclear, ask for revised wording or an endorsement. Look for service commitments around response times, breach counsel access, and data restoration support. A policy that pairs funding with fast access to the right experts is among the most valuable options in a crisis.
If an incident occurs, notify your insurer quickly—early contact unlocks coordinated counsel and forensics, helps preserve evidence, and avoids missteps that can complicate recovery. Typical steps include isolating affected systems, engaging legal guidance, initiating forensic imaging, restoring from clean backups, and coordinating regulatory notifications within required timelines. Keep a simple communications plan to update staff, customers, and partners without speculation. Document costs as they arise; clear records speed reimbursement.
Final takeaways for small business owners: treat cyber insurance as one component of resilience. Strong controls reduce both risk and price; good wording prevents surprises; a tested plan compresses downtime. You do not need to be perfect to be protected—just deliberate. Start with MFA and backups, choose a limit tied to your realistic downtime math, and secure terms that fit how you actually work. With that foundation, a policy becomes a stabilizer rather than a gamble, ready to help when you need time, expertise, and calm in the storm.


